Armitage Post Exploitation
a11y.text Armitage Post ExploitationOften times, penetration testers get too carried away with their initial shell that they forget to perform a thorough check on the machine. They could be attacking a honeypot and would not even know it. This is why post-exploitation is essential to every penetration test. Let us explore how we can run post exploitation modules through Armitage.
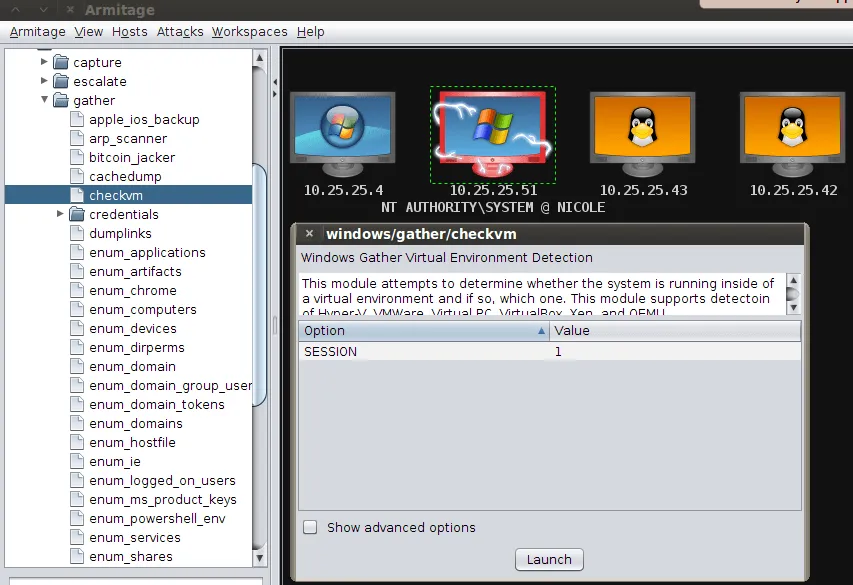
With shell access to the machine, post exploitation becomes relatively easy. We simply select the post exploitation module we’d like to run by double-clicking on it, and then click on ‘Launch’.
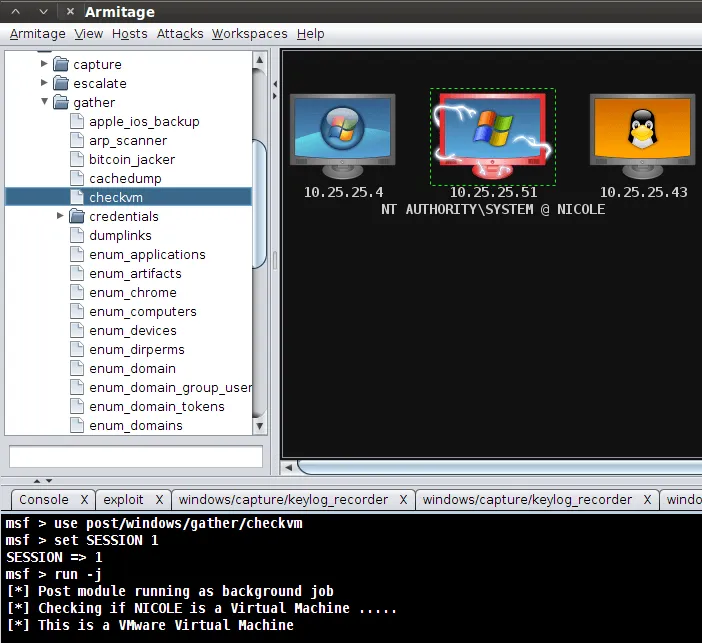
We then sit back and enjoy our margaritas while Armitage works its magic. In this particular case, Armitage ran a post exploitation module for us and determined the machine we were attacking is a VMware virtual machine.
Penetration testers have many post-exploitation modules at their disposal. Learning how to use them will set you apart from the rest!