
As part of the Cybersecurity Awareness Month 2022, we share a complete guide to starting a career as a penetration tester.

As part of the Cybersecurity Awareness Month 2022, we share a complete guide to starting a career as a penetration tester.

Jeremy "Harbinger" Miller shares with us his thoughts on cognitive biases and how they relate to penetration testing.

Hear directly from Offensive Security’s experts on the latest course releases, and the infosec topics that interest our community.
Take a look back at 2020’s course launches and updates, and learn what to expect in 2021 with this year-end recap from Offensive Security.

Learn how Packetlabs used Offensive Security’s Proving Grounds solution to identify and hire top penetration testing talent.

How can source code review help penetration testers with web application security assessments? Learn the benefits of white box web app penetration testing.

Donavan Cheah gives us some of his thoughts on the subject of penetration testing, and his journey with the AWAE course in particular.

OffSec student Christopher M Downs takes trying harder to another level: completing (and passing) his OSCP exam in the middle of a New Orleans flood. Read more about Christopher's inspiring journey.

Samuel Whang, a PWK graduate, details his recommendations and a unique philosophical approach for those looking to pursue their OSCP. This article originally appeared on Sep 24, 2019, posted by Samuel Whang. It has been posted with minor edits, with permis
In our last blog post, we provided an example of running an unattended network installation of Kali Linux. Our scenario covered the installation of a custom Kali configuration which contained select tools required for a remote vulnerability assessment using Op

It’s been 7 years since we released our first version of BackTrack Linux, and the ride so far has been exhilarating. When the dev team started talking about BackTrack 6 (almost a year ago), each of us put on paper a few “wish list goals” that we each wan
In one of our recent engagements, we had the opportunity to test the physical security of an organization. This assessment presented an excellent scenario for a USB HID attack, where an attacker would stealthily sneak into a server room, and connect a maliciou
... Read more »
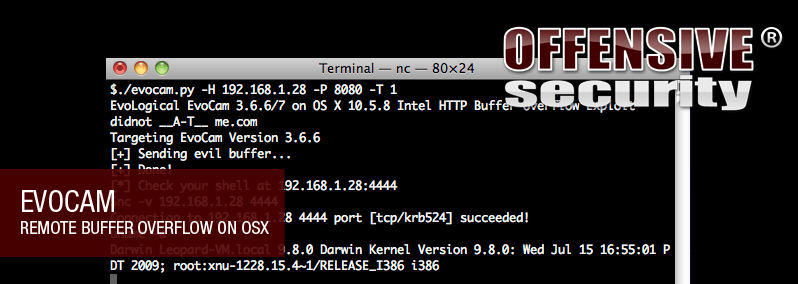
This guide comes from my own journey from finding a buffer overflow in an OS X application to producing a working exploit. I have reasonably good exploit development skills having completed the Penetration Testing with BackTrack and Cracking the Perimeter trai

As promised, we are releasing a BackTrack 4 R1 information security and penetration testing development build to the public for hardware testing.
The release of BackTrack 4 unleashed a whirlwind of over 1 million downloads. Information Security specialists and Penetration Testers from all over the world showing their support and love for the product that has become the #1 Penetration Testing Distribut