OffSec student 0xklaue wrote this review of Advanced Web Attacks and Exploitation and the OSWE exam. Find out how to prepare and what you need to know.
OffSec student 0xklaue wrote this review of Advanced Web Attacks and Exploitation and the OSWE exam. Find out how to prepare and what you need to know.

Meet Mihai, a 16 year old OSCP holder and PWK graduate out of Romania. Read more about his tremendous start and journey into infosec.

OffSec student Christopher M Downs takes trying harder to another level: completing (and passing) his OSCP exam in the middle of a New Orleans flood. Read more about Christopher's inspiring journey.

Samuel Whang, a PWK graduate, details his recommendations and a unique philosophical approach for those looking to pursue their OSCP. This article originally appeared on Sep 24, 2019, posted by Samuel Whang. It has been posted with minor edits, with permis
Today we all constantly read about data breaches that could have been prevented if the impacted organization had just done what they were supposed to do. The unfortunate reality is that cyberattacks are now a matter of 'when' and not 'if' for the average enter
It’s been a busy few months for us here, and for good reason. Today we are proud to announce our new partners at Offensive Security - Spectrum Equity.

Seven years of developing BackTrack Linux has taught us a significant amount about what we, and the security community, think a penetration testing distribution should look like. We've taken all of this knowledge and experience and implemented it in our "next
Offsec has teamed up with the crew at Hackers For Charity and the world's premier Hacker Con - BlackHat, to provide another amazing cyber hacking challenge.
A new report by emgent shows malicious Google Gadgets in action. The vulnerability lies in the ability of a malicious user to add their own Gadgets on a separate domain space, without Google's authorization. The attack variant shown in the movie can be altered

BlackHat Offensive Security Training Courses are selling out...sign up quick! To all those who signed up - we've got some special things planned for you, you're definitely in for a ride. Thanks for flying Offsec.

Penetration Testing with BackTrack v3.0 now available and better than ever!
Today (as promised in part 1 of the QuickZip Stack BOF exploit write-up), I will explain how to build the exploit for the quickzip vulnerability using a pop pop ret pointer from an OS dll. At the end of part 1, I challenged you, the Offensive Security Blog r
Penetration Testing with BackTrack updates
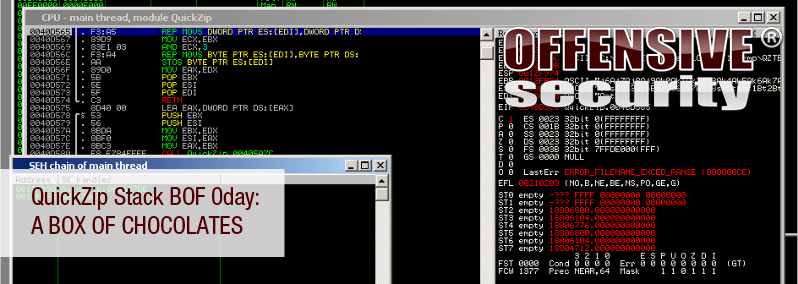
A few days ago, one of my friends (mr_me) pointed me to an application that appeared to be acting somewhat “buggy” while processing “specifically” crafted zip files. After playing with the zip file structure for a while (thanks again, mr_me, for docu

The Offensive Security team is excited to announce the release date of v3.0 of the Pentesting With BackTrack Course. On March 21, 2010 the course will be made live. The team has worked overtime to ensure the videos and labs are better than ever. With new mod
After a short and intense setup, we are ready to present the Offsec Exploit Archive. We’ve recreated the milw0rm database, updated it and are now accepting submissions. The purpose of the site is to provide researchers and security enthusiasts a reposito