Research & Tutorials
OffSec experts share cutting-edge vulnerability research, tool reviews, tutorials, virtual lab and content walkthroughs.
Mar 12, 2025
4 min read
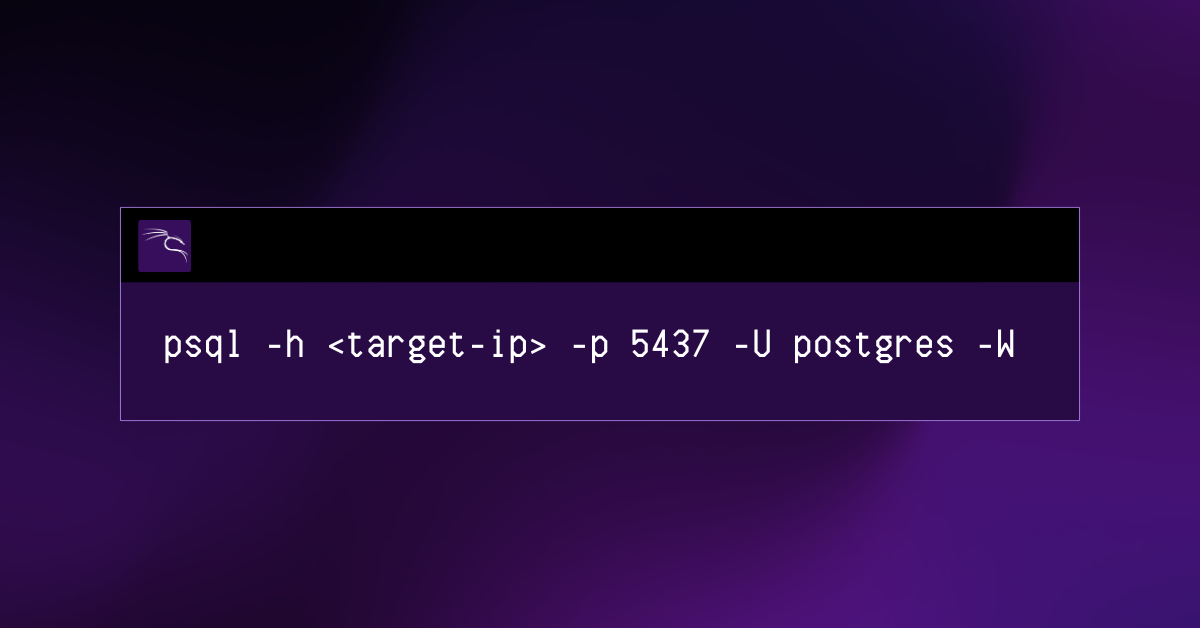
PostgreSQL Exploit
Sharpen your hacking skills! Learn from our walkthrough of a PostgreSQL exploit in the Nibbles machine on PG Practice.

Research & Tutorials
CVE-2025-21298: A Critical Windows OLE Zero-Click Vulnerability
Explore CVE-2025-21298, a critical Windows OLE zero-click flaw enabling RCE via email. Learn its risks, impact, and how to defend against attacks.
Feb 3, 2025
3 min read
Research & Tutorials
My Journey with IR-200: Becoming an OffSec Certified Incident Responder (OSIR)
Embark on a journey to become an OffSec Certified Incident Responder (OSIR) through the IR-200 course, as described by a Student Mentor who tested its effectiveness.
Jan 24, 2025
6 min read
Research & Tutorials
A Student Mentor’s TH-200 and OSTH Learning Experience
Explore the TH-200 course & OSTH exam with an OffSec Mentor’s insights on mastering threat hunting skills.
Jan 24, 2025
9 min read
Research & Tutorials
Post-quantum Cryptography in 2024
Explore post-quantum cryptography’s rise in 2024 and how new standards prepare us for future quantum attacks, ensuring secure data.
Aug 22, 2024
9 min read

Research & Tutorials
How to Become a Cybersecurity Engineer
Learn how to become a cybersecurity engineer, including the educational paths to follow, the crucial skills and certifications needed, and more.
Aug 8, 2024
11 min read

Research & Tutorials
RegreSSHion exploit, CVE-2024-6387: A Write-Up
In this blog post, we will be explaining the new RegreSSHion exploit, CVE-2024-6387 and how it works.
Jul 8, 2024
9 min read
Research & Tutorials
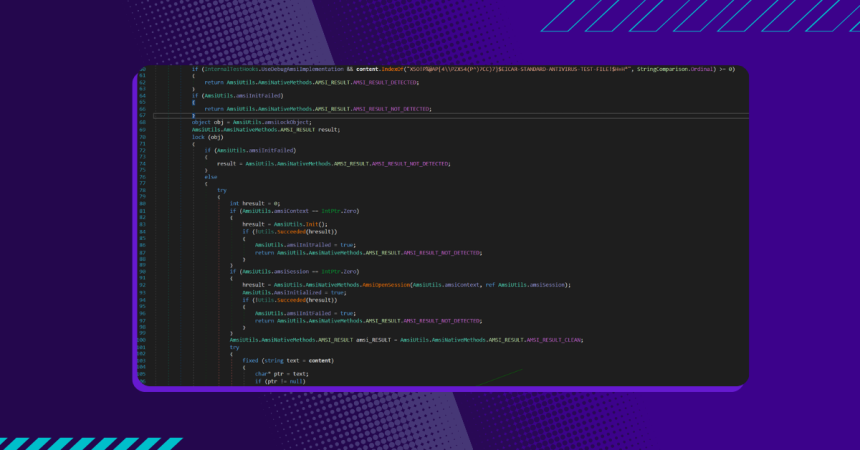
AMSI Write Raid Bypass Vulnerability
In this blog post, we’ll introduce a new bypass technique designed to bypass AMSI without the VirtualProtect API and without changing memory protection.
May 3, 2024
14 min read

Research & Tutorials
Behind Enemy Lines: Understanding the Threat of the XZ Backdoor
The following is an excerpt from our new module on the recent XZ Utils backdoor, CVE-2024-3094. On Mar 29, 2024, at 12:00PM ET, Andres Freund posted on the Openwall mailing list about a backdoor he discovered in the XZ Utils package. The backdoor targeted the OpenSSH binary, allowing remote code execution on impacted machines.
Apr 9, 2024
5 min read

Research & Tutorials
How Is AI Used in Cybersecurity?
Learn how AI is used in cybersecurity for threat detection, security operations, and defense. Explore generative AI risks and practical integration steps.
Feb 26, 2024
9 min read

Research & Tutorials
Ransomware Revealed: From Attack Mechanics to Defense Strategies
Explore the evolution of ransomware attacks, their impact, types, and learn robust defense strategies against this escalating cyber threat.
Dec 15, 2023
8 min read

Research & Tutorials
Social Engineering: The Art of Human Hacking
Learn how social engineering exploits human vulnerabilities through manipulation and deception. This guide covers different tactics cybercriminals use and key strategies to protect your organization.
Dec 8, 2023
7 min read

Research & Tutorials
Advanced Persistent Threats: OffSec’s Comprehensive Guide
Explore key strategies to safeguard against Advanced Persistent Threats (APTs), focusing on prevention, response, and recovery in cybersecurity.
Nov 28, 2023
7 min read
Join the OffSec Community!
Our community members connect, communicate and collaborate on all things cybersecurity