Blog
News and updates from OffSec

Feb 15, 2011
MSFU Updates – February 2011
This past month has seen a number of additions to our free Metasploit Unleashed training course, primarily in our on-going effort to build out the Metasploit Module Reference section. In addition, we are still continuing to work through the course content to ensure that it is still all functional.
Categories

Kali Linux
MSFU Updates – January 2011
This past month has seen a number of additions to our free Metasploit Unleashed training course, primarily in our on-going effort to build out the Metasploit Module Reference section. The Metasploit team has been developing at a rapid pace with new features and modules being frequently added. We are also continuing to go through the course content itself and verify the functionality of the provided material.
Jan 17, 2011
1 min read
Research & Tutorials
The Art of Human Hacking
It’s hard to believe that the social-engineer.org project began 14 months ago. This project started from a simple idea to build the world’s first framework for social engineers. In these 14 months, this project has grown into the leading resource for all real social engineering education. The CTF that we held at Defcon 18 proved beyond doubt that this resource was greatly required.
Dec 19, 2010
2 min read

Kali Linux
MSFU Updates – December 2010
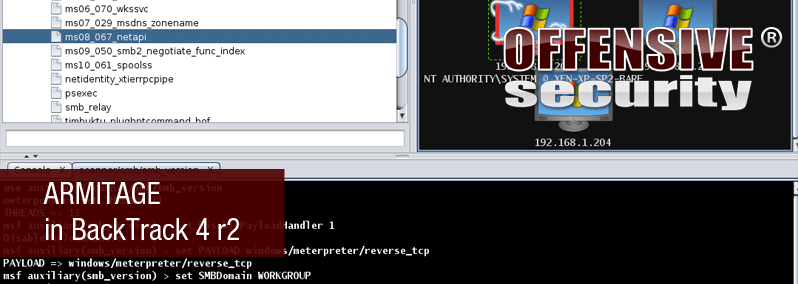
This month we have again been steadily updating the Metasploit Module Reference section of Metasploit Unleashed and also added some great new content covering the setup and usage of databases with Metasploit under BackTrack4 R2. This month also saw the introduction of the excellent GUI front-end, Armitage.
Dec 15, 2010
1 min read
Kali Linux
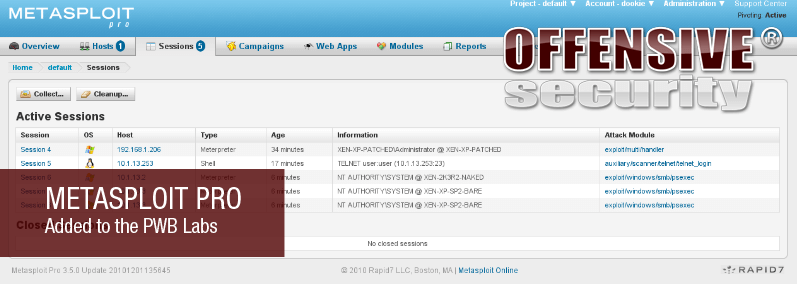
Metasploit Pro Added to the PWB Labs
We are very happy to announce that our Penetration Testing with BackTrack online labs now include installations of Metasploit Pro. Deep within our lab network, students who Try Harder™ will encounter credentials for these installations that will allow them to enjoy the use of a tool that simplifies many of the tasks that they had to perform manually.
Dec 13, 2010
6 min read
Research & Tutorials
Godaddy Workspace XSS – Who’s your Daddy ?
An interesting submission in from the Exploit Database – a Godaddy workspace XSS vulnerability. Although we did not post it (live site), the vulnerability seems real, and definitely worth mentioning.
Dec 11, 2010
1 min read
Kali Linux
Armitage in BackTrack 4 r2
A brief time ago, an exciting GUI front-end for Metasploit named Armitage was released. For being an initial release, Armitage is very polished and so we knew we had to add it to the BackTrack respositories.
Nov 29, 2010
3 min read

Kali Linux
Metasploit with MySQL in BackTrack 4 r2
Until the release of BackTrack 4 r2, it was possible to get Metasploit working with MYSQL but it was not an altogether seamless experience. Now, however, Metasploit and MYSQL work together “out of the box” so we thought it would be great to highlight the integration. With the Metasploit team moving away from sqlite3, it is vital to be able to make use of a properly threaded database. There have also been quite a number of additional database commands added to Metasploit and documentation tends to be rather sparse online when it comes to the less “glamorous” side of database management.
Nov 21, 2010
7 min read

Kali Linux
MSFU Updates – November 2010
This past month has been busy yet we have been steadily updating the free Metasploit Unleashed Training course with the largest growing area being the Module Reference section. This month has also seen updates to the Fast-Track and Social-Engineer Toolkit sections of the wiki.
Nov 15, 2010
1 min read
Exploit Development
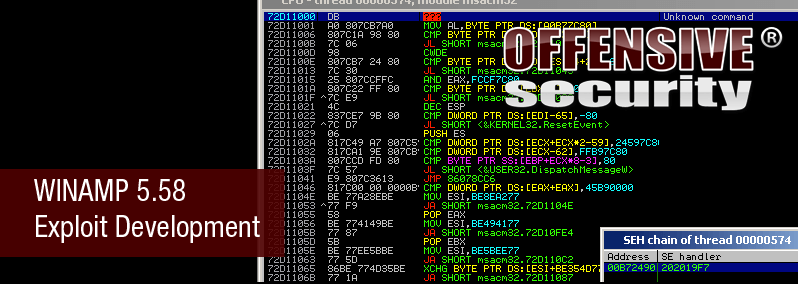
Winamp 5.58 Exploit Development
The guys at the Exploit Database posted an awesome writeup on a Winamp 5.58 Exploit Development storming session – with some really cool results. In the end, they ended up writing a short assembly sequence to walk through the payload and replace bad characters with original shellcode bytes.
Oct 27, 2010
1 min read
Exploit Development
Adobe Shockwave player rcsL chunk memory corruption 0day
Adobe Shockwave player rcsL chunk memory corruption 0day demonstration and video
Oct 21, 2010
1 min read

Kali Linux
Metasploit Unleashed, Again!
Metasploit Unleashed – new wiki with updated materials
Oct 6, 2010
2 min read

Kali Linux
Metasploit Unleashed – Updates
Updates to the Metasploit Unleashed Free online Training course, by Offensive Security.
Aug 26, 2010
1 min read
Join the OffSec Community!
Our community members connect, communicate and collaborate on all things cybersecurity