
Oct 12, 2022
See Yourself in Cyber with OffSec: Security Operations
As part of Cybersecurity Awareness Month 2022, we share a complete guide to starting a career in security operations and defense.
Pursuing a career in cybersecurity means joining a booming and diverse industry. There are many opportunities for individuals entering the field to find a career path suited to their interests and skill set.
With a high-demand for workers and a lower barrier to entry when transition from other fields, security operations and defense is a good career path for many looking to break into the industry.
What is a security operations center?
Organizations need a consistent and continuous method to defend their systems and networks through monitoring, detection, and analysis of cyber threats. An effective defensive security strategy implemented by mature organizations is a Security Operations Center or SOC.
A security operations center (SOC) is a team of security professionals who monitor an organization’s IT infrastructure 24/7, operate and maintain defensive security technology and tools, and continuously analyze threat data in real-time to address security events as quickly as possible. The primary role of the SOC team is to detect, analyze and respond to security incidents and improve an organization’s security.
SOC teams can be an in-house team but they can also be an external, outsourced team. There are also scenarios of a hybrid SOC team where some activities are performed by an in-house team, while others are outsourced which is a solid solution for mid-range and even some larger companies.
Security operations tasks and responsibilities
A SOC team has many responsibilities and juggles multiple tasks that include technical and analytical areas. While the primary duty of the SOC team is to defend an organization against cyber attacks, their day-to-day tasks and responsibilities also include:
- Continuous proactive monitoring
- Investigating suspicious activity and alerts
- Prioritizing detected security incidents
- Triaging incidents to minimize risk
- Incident response
- Managing defensive security tools that include firewalls, intrusion detection and prevention, vulnerability management, log collection, security information and event management (SIEM), endpoint detection and response (EDR), and reporting tools, among others
- Log management
- Effectively communicating and reporting key findings to management
Security operations career path
While not all SOCs are operated in the same manner, they usually consist of security analysts, incident responders, threat hunters, malware analysts, security engineers, and SOC managers.
Security analysts detect, analyze and respond to threats. There are usually 3 Tiers in most organizations. Tier 1 analysts are entry-level and usually, monitor the network, and investigate and prioritize security alerts. Tier 2 analysts are usually the incident responders and Tier 3 analysts are also known as threat hunters that comb through data to search for hidden suspicious activity and uncover threats not flagged by automated tools.
Security engineers build and maintain the defensive security architecture and systems and
SOC managers oversee and manage the team and are responsible for hiring and training SOC staff.
Why choose a job in security operations and defense?
A security operations center plays a central role in modern enterprise cybersecurity. Cybersecurity professionals in a SOC act as the first line of cyber defense and protect their organization and its critical systems. And with such a variety of different roles on the defensive side, there is a huge demand for professionals to fill these roles.
If you’re at the beginning of your career and hoping to specialize, you’re will find it much easer to find a job in security operations. It’s also easier to transition to the defensive side. For example you can start out as a system administrator, and then begin learning about system hardening, start paying attention to logs and network traffic, and go from there.
Working in a SOC can offer you a fast-paced, highly collaborative, and stimulating career path. With plenty of opportunities for continuous learning and advancement to senior roles, if you have a passion for fighting cybercrime and investigating cyber incidents a career in security operations can be the ideal path for you. Furthermore, it’s a financially rewarding career path. The average base salary of the more entry-level roles such as the SOC analyst Tier 1 is reported to be $86,855 per year, and $112,594 for Threat Hunters. Senior SOC Analysts can earn up to $158,000 per year.
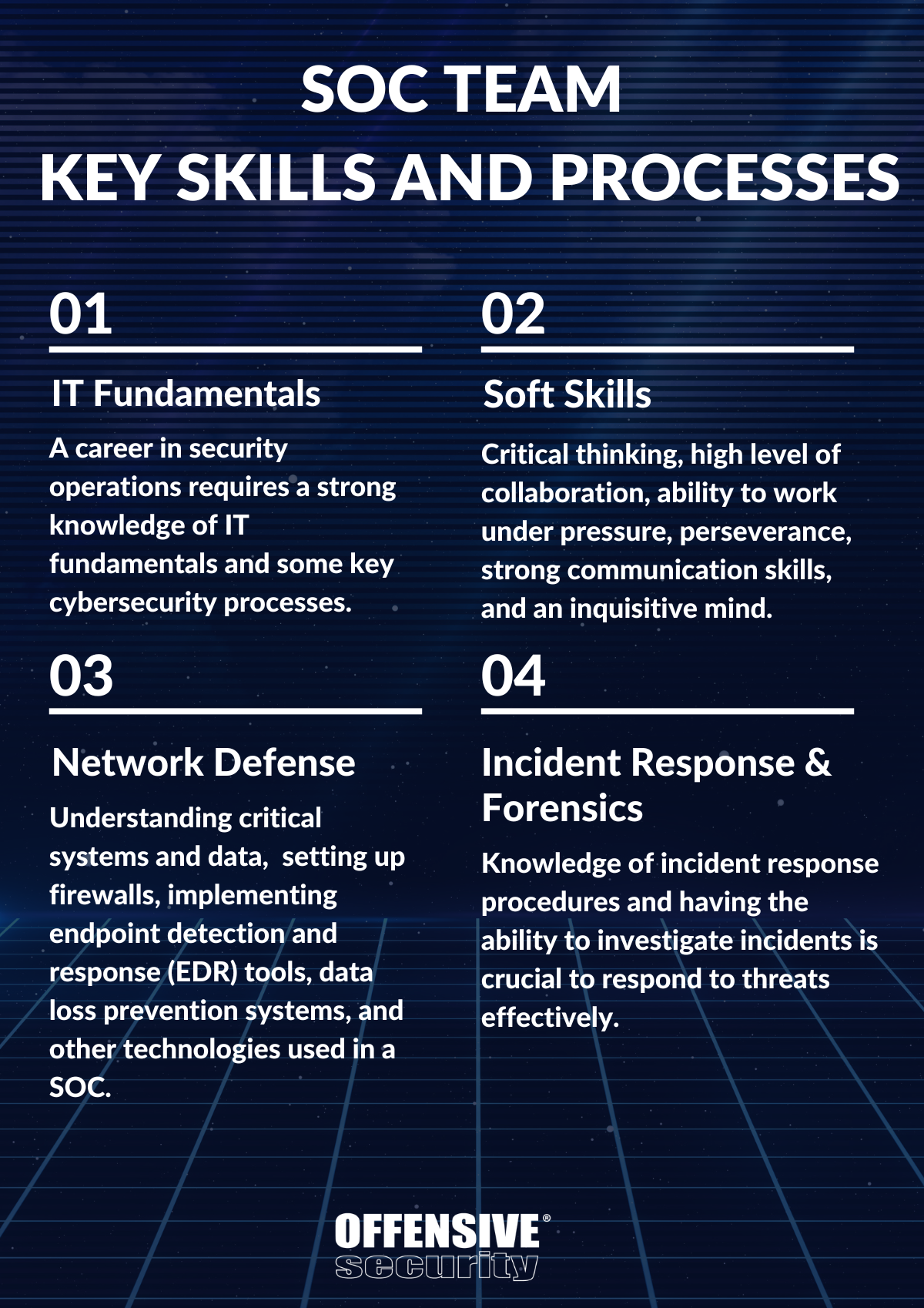
Key skills and processes in security operations and defense
While a SOC employs a vast array of technology and automated tools, a technically proficient and skilled SOC team is essential to defend the organization from all types of cybercrime. Some of the key skills for professionals seeking a career in security operations include:
- Strong IT fundamentals
When starting in any cybersecurity domain, a career in security operations also requires a strong knowledge of fundamental IT concepts. Ensure you have a solid command over fundamental IT concepts, such as IT infrastructure, applications and software, operating systems, databases as well as some key cybersecurity processes and basics of networking.
Learn Fundamentals is the ideal cybersecurity training plan for those looking to get their initial foothold with an entry-level role. Diverse content covers all technical-adjacent topics needed to start your cybersecurity career, and the SOC-100 training will offer you all the needed prerequisite knowledge to start working towards your first entry-level role in security defense.
- Network defense
As a defensive security approach, a career in security operations requires a mastery of network defense skills. A wide range of technologies and activities is involved in network defense, including reducing the organization’s attack surface, understanding critical systems and data, but also setting up firewalls, implementing endpoint detection and response (EDR) tools, data loss prevention systems, and other technologies used in a SOC.
- Incident response
While prevention and being proactive with cyber threats is the goal of any cybersecurity program, being reactive and responding to threats swiftly when they occur is crucial in minimizing potential damage. Knowledge and understanding of the formal incident response process and procedure is crucial for responding to cyber threats in a timely and effective manner.
- Digital forensics
While more commonly required for higher-level SOC roles, digital forensics is an important part of responding to threats. When the SOC detects an incident, they launch incident response and an investigation that includes digital forensics, in order to determine the nature of the threat and find out more about what happened. Investigating and gathering evidence on the origin of the threat and the attack path will help analysts to better understand how to properly respond and contain an incident.
- Soft skills
Hard technical skills can be taught, but in order to pursue a career in security operations, a set of soft skills are a must for an individual to possess. Critical thinking might just be the soft skill needed for any domain of cybersecurity, but it’s incredibly important for SOC teams. Looking at all of the alerts produced by their tools and prioritizing them, understanding threats, and applying logic on how to respond to them are all important for the day-to-day functioning of a SOC team.
As working in security operations include working in a team, it’s important to garner a high level of collaboration. Working together is vital for properly and quickly determining the threat and how to respond to it.
Security operations is a notably stressful field. Providing continuous monitoring and detection using a vast number of tools that produce alerts combined with the need to determine what alerts are false positives and which require your attention, can lead to alert fatigue and lapse of judgment in responding to threats. This is why being able to work under pressure and being resistant in a high-stress environment is one of the more important skills for individuals looking for a career in security operations.
Good communication skills and the ability to explain technical concepts and findings to a non-technical audience are also imperative in order to properly report to management.
And just as with many, if not all, cybersecurity careers, an inquisitive mind that constantly looks for a way to reinforce and advance their skills and knowledge is a prerequisite for any cyber defense role.
Get your start in security operations
Commonly, a requirement for an entry level role in a defensive team requires a degree in computer science or engineering, but hands-on experience in an IT or networking role such as system administration and system hardening can also help you when pursuing a career in security operations. Once you’ve gained the security defense and operations key skills, it’s always good to seek additional training to continuously improve your skills and mastery of tools.
Certifications are also becoming increasingly important for employment in security operations, so enrolling in industry-recognized training and earning valuable certifications is a good step in your pursuit of this career.
Offensive Security’s Security Operations and Defensive Analysis (SOC-200) course is designed to empower students with knowledge of the consequences of common attacks from a defensive perspective. In this course, you will learn how attackers operate using recognized frameworks, how to audit Windows and Linux endpoints, review common attacks, use a SIEM, and much more! SOC-200 is designed for job roles such as SOC Analysts, Junior Threat Hunters, and Threat Intelligence Analysts as well as Junior roles in Digital Forensics and Incident Response.
Students who complete the course and pass the associated exam earn the Offensive Security Defense Analyst (OSDA) certification, demonstrating their ability to detect and assess security incidents.
A career on the defensive side of cybersecurity is an attractive option with the notoriously high salaries and abundance of jobs across various roles. It can be a highly rewarding choice for those interested in investigating and protecting against cyber threats.
The right combination of technical skills, mastery of key cybersecurity concepts and technologies, soft skills, and industry-recognized training and certification can set you up for a fruitful and successful career in security operations.

Sara Jelen
Sara Jelen is the Content Marketing Manager at OffSec. Through her extensive work as a writer and content marketer, Sara is specialized in the cybersecurity domain. With a background in anthropology and arts, Sara incorporates a human-centric perspective in exploring cybersecurity topics and the movers and shakers behind it.
Stay in the know: Become an OffSec Insider
Get the latest updates about resources, events & promotions from OffSec!
Latest from OffSec

Research & Tutorials
CVE-2025-27636 – Remote Code Execution in Apache Camel via Case-Sensitive Header Filtering Bypass
Discover the critical Apache Camel vulnerability (CVE-2025-27636) that allows remote code execution via case-sensitive HTTP header manipulation in the exec component. Learn how attackers exploit this flaw and how to mitigate it.
Jul 10, 2025
2 min read

Research & Tutorials
CVE-2025-29306 – Unauthenticated Remote Code Execution in FoxCMS v1.2.5 via Unserialize Injection
Discover details about CVE-2025-29306, a critical RCE vulnerability in FoxCMS 1.2.5. Learn how unsafe use of PHP’s unserialize() function enables remote attackers to execute arbitrary system commands.
Jul 3, 2025
2 min read

Research & Tutorials
CVE-2024-39914 – Unauthenticated Command Injection in FOG Project’s export.php
Discover details about CVE-2024-39914, a critical unauthenticated command injection vulnerability in FOG Project ≤ 1.5.10.34. Learn how attackers can exploit export.php to execute system commands or deploy persistent webshells.
Jun 26, 2025
2 min read